North Korea stole $620 million in cryptocurrency from hacking a game company in March, which was likely used to fund the launching of dozens of ballistic missiles it fired in the first half of this year, Seoul’s special envoy for North Korea said Thursday.
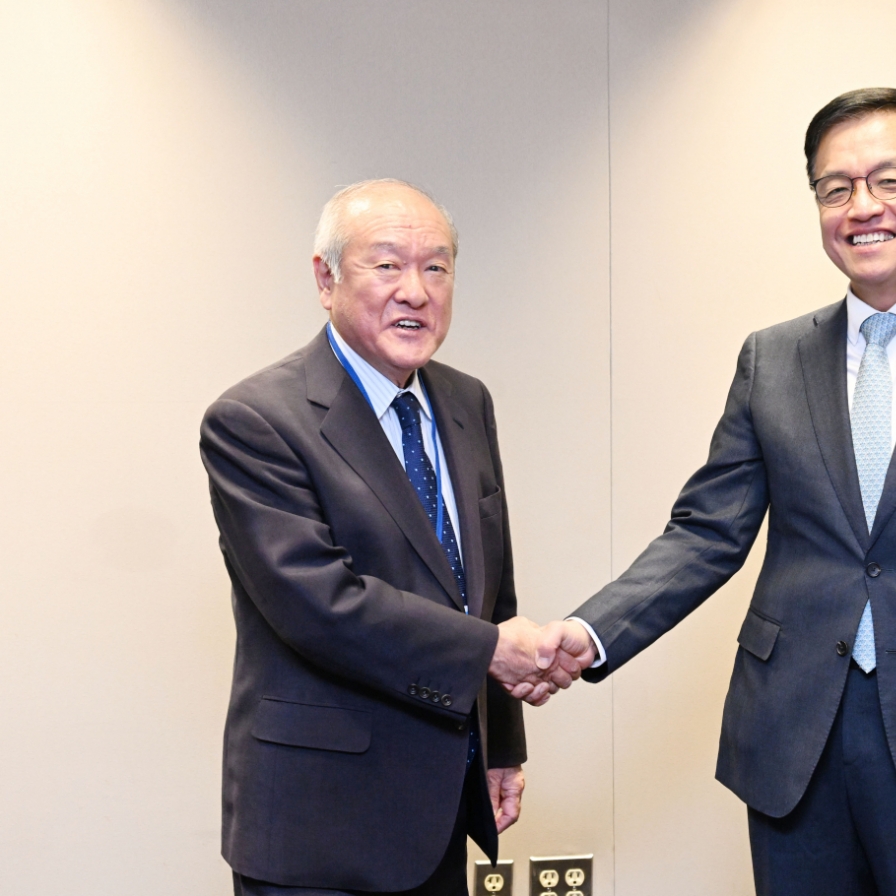
Speaking at a symposium on North Korea’s cyber threats jointly held by the Ministry of Foreign Affairs and the US State Department for the first time, Kim Gunn, special representative for Korean Peninsula peace and security affairs, said Pyongyang is likely to have spent about $400 million to $650 million to launch 31 ballistic missiles in the first half of this year.
The special envoy suggest the fund Pyongyang stole from one of its latest and the biggest cyber scam case this year would likely have contributed to the missile launches. The North Korean regime is suspected of having stolen more than $620 million in cryptocurrency from online video game Axie Infinity in March.
Through Thursday, North Korea had fired an unprecedented number of ballistic missiles at more than 65, with the latest coming the same day.
In the symposium, Jung Pak, US deputy special representative for North Korea, explained how cryptocurrency exchanges and blockchain companies provide Pyongyang with "a lucrative arena" to engage in malicious cyber activity -- not only to bypass the international financial system and evade United Nations sanctions, but also to fund its growing weapons program.
“The DPRK is one of just a few countries in the world and definitely the most egregious that is actively stealing money from other countries, their companies and their people,” Pak said, referring to North Korea's official name, Democratic People’s Republic of Korea.
She also raised concerns that Pyongyang targets developing countries precisely as they have not yet developed robust cyberdefenses.
About the North’s cryptocurrency heist in March, which she said is the largest on record, the regime would likely have used the fund to procure materials for its unlawful weapons of mass destruction and ballistic missile programs, she said.
“The United States has taken steps to curtail the DPRK malicious cyber activities and thereby impede its weapons development. … We have imposed sanctions on DPRK cyber actors and those facilitating their malicious activities, and have worked to build our partners capacity to defend against this threat,” Pak said.
“It is vital for governments, network defenders and the public to stay vigilant and to work together to mitigate the cyber threat posed by the DPRK.”
Director General for North Korean Nuclear Affairs Lee Tae-woo of South Korea's Foreign Ministry said North Korea appears to have collected about $1 billion of cryptocurrency from January to July, citing a report released this year.
“North Korea’s illegal cyber activities should not be taken simply as a financial crime. North Korea’s foreign currency is used directly to develop nuclear missiles,” Lee said.
“So the measures to handle North Korea’s cyber threats means more than just preventing financial damage, it is for the peace and stability of the international society.”
The day before, South Korea and the US held a second working group meeting on North Korean cyber threats in Seoul, where they agreed to strengthen cooperation, with Lee Tae-woo and Jung Pak leading the respective delegations.
North Korea has been observed increasing number of hacking cases around the world.
In 2014, hackers Thought to be connected to the North Korean government broke into Sony Pictures Entertainment to steal confidential documents and reveal them online. In 2017, 48 entities in Britain, mainly hospitals, were affected by ransomware cyberattacks in which criminals behind the assault were observed to have raised just some $20,000, though causing losses and costs estimated at well over $100 million.
In Thursday's symposium, some 200 attended the symposium, which brought government officials from 16 countries and others from the private sector, including cryptocurrency experts and blockchain firms, according to Seoul's Foreign Ministry.
By Jo He-rim (herim@heraldcorp.com)